Malware analysis is a critical field within cybersecurity that focuses on understanding malicious software, its behavior, and its impact on systems and networks. As cyber threats continue to evolve, the need for effective malware analysis has become paramount for organizations seeking to protect their digital assets. Malware, short for malicious software, encompasses a wide range of harmful programs, including viruses, worms, trojans, ransomware, and spyware.
Each type of malware has its own unique characteristics and methods of operation, making it essential for analysts to develop a comprehensive understanding of these threats. The primary goal of malware analysis is to dissect and comprehend the inner workings of malicious code. This involves identifying the malware’s origin, its intended purpose, and the potential damage it can inflict.
By analyzing malware, cybersecurity professionals can develop strategies to detect, mitigate, and prevent future attacks. Furthermore, insights gained from malware analysis can inform the development of security tools and protocols, ultimately enhancing an organization’s overall security posture. As cybercriminals become increasingly sophisticated in their tactics, the importance of thorough malware analysis cannot be overstated.
Key Takeaways
- Malware analysis is the process of examining malware to understand its behavior and functionality.
- Understanding malware behavior is crucial for developing effective defense mechanisms and mitigating potential threats.
- Tools and techniques for malware analysis include sandboxing, disassemblers, debuggers, and network sniffers.
- Dynamic malware analysis involves observing the behavior of malware in a controlled environment to understand its impact.
- Static malware analysis involves examining the code and structure of malware without executing it.
Understanding Malware Behavior
Malware Persistence
Understanding these behaviors allows analysts to categorize malware and predict its potential impact on targeted systems. One common behavior exhibited by malware is persistence. Many types of malware are designed to remain on a system even after a user attempts to remove them. This can be achieved through various techniques, such as modifying system files or creating new registry entries that ensure the malware is reloaded upon system reboot.
Evasion Techniques
Additionally, some malware employs stealth techniques to evade detection by antivirus software or other security measures. For example, rootkits can hide their presence by manipulating system processes and files, making it challenging for analysts to identify and remove them.
Communication with External Servers
Another critical aspect of malware behavior is its communication with external servers. Many modern malware variants are designed to connect to command-and-control (C2) servers to receive instructions or exfiltrate stolen data. This communication can occur through various protocols, including HTTP, HTTPS, or even peer-to-peer networks.
Understanding these behaviors not only aids in the identification of specific malware strains but also helps in developing effective countermeasures.
Tools and Techniques for Malware Analysis

The field of malware analysis is supported by a wide array of tools and techniques that facilitate the examination of malicious software. These tools can be broadly categorized into static analysis tools and dynamic analysis tools. Static analysis involves examining the code of the malware without executing it, while dynamic analysis entails running the malware in a controlled environment to observe its behavior in real-time.
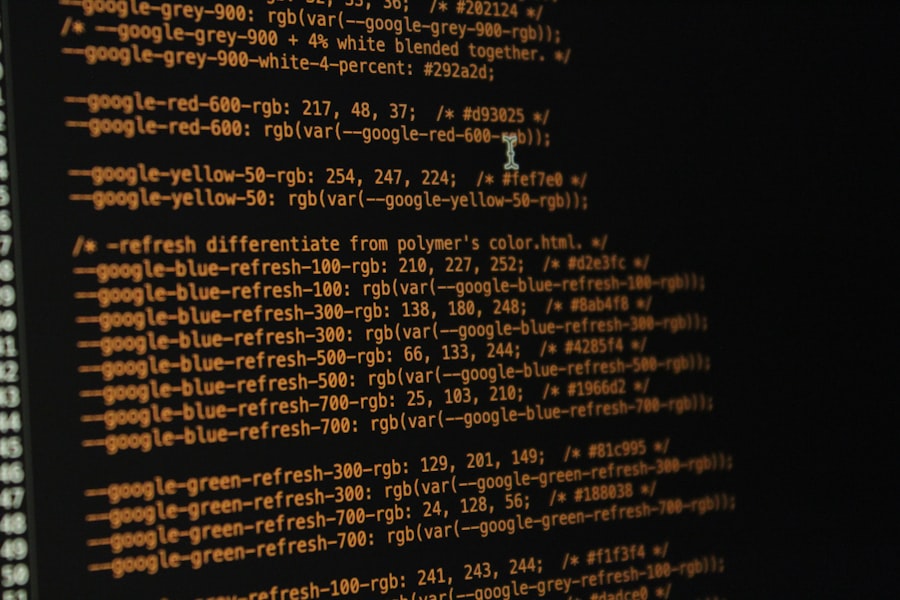
Static analysis tools often include disassemblers and decompilers that convert machine code into human-readable formats. Tools like IDA Pro and Ghidra are popular choices among analysts for their ability to provide detailed insights into the structure and functionality of malware. Additionally, hash analysis tools can be employed to identify known malware samples by comparing their hashes against databases of previously analyzed threats.
This can significantly speed up the identification process and help analysts focus on new or unknown variants. Dynamic analysis tools are equally important in the malware analysis process. Sandboxes such as Cuckoo Sandbox allow analysts to execute malware in a safe environment where its behavior can be monitored without risking damage to actual systems.
These tools capture various metrics, including file system changes, network traffic, and process creation, providing a comprehensive view of how the malware operates. By combining both static and dynamic analysis techniques, analysts can develop a more complete understanding of the malware’s capabilities and potential impact.
Dynamic Malware Analysis
Dynamic malware analysis is a crucial component of understanding how malicious software behaves in real-world scenarios. This approach involves executing the malware in a controlled environment—often referred to as a sandbox—to observe its actions and interactions with the operating system and network. The primary advantage of dynamic analysis is that it allows analysts to see firsthand how the malware operates, including any changes it makes to files or system settings.
During dynamic analysis, various behaviors can be monitored in real-time. For instance, analysts can track file system modifications, registry changes, and network communications initiated by the malware. This information is invaluable for understanding the full scope of the threat.
For example, if a piece of ransomware is executed in a sandbox environment, analysts can observe how it encrypts files and communicates with its C2 server to demand payment from victims. Such insights are critical for developing effective detection mechanisms and response strategies. Moreover, dynamic analysis can reveal evasion techniques employed by sophisticated malware.
Some malicious programs are designed to detect when they are running in a virtualized environment and may alter their behavior accordingly—either by becoming dormant or by executing only benign actions to avoid detection. Analysts must be aware of these tactics and employ advanced techniques to ensure that they capture accurate data during dynamic analysis sessions. This may involve using anti-evasion techniques or employing multiple layers of monitoring to ensure comprehensive visibility into the malware’s behavior.
Static Malware Analysis
Static malware analysis serves as a foundational technique in the field of cybersecurity, allowing analysts to examine malicious code without executing it. This method involves dissecting the binary code of the malware to uncover its structure, functionality, and potential indicators of compromise (IOCs). Static analysis is particularly useful for identifying known vulnerabilities or malicious patterns within the code that could indicate its purpose.
One of the primary tools used in static analysis is disassembly software, which translates machine code into assembly language or higher-level programming languages. Tools like Radare2 or Binary Ninja enable analysts to navigate through complex code structures and identify key functions that may be responsible for malicious activities. By examining these functions, analysts can gain insights into how the malware operates and what specific actions it may take once executed.
This information can provide clues about the origin of the malware or its intended target. For example, certain file signatures may indicate that a piece of malware was developed using specific programming languages or frameworks commonly associated with particular threat actors.
By correlating this data with known threat intelligence sources, analysts can build a more comprehensive picture of the threat landscape.
Reverse Engineering Malware
Disassembling the Code
The reverse engineering process often begins with disassembling the binary code using specialized tools like IDA Pro or Ghidra. Once the code is disassembled, analysts can trace through function calls and data flows to identify how the malware interacts with system resources.
Uncovering Hidden Functionalities
Reverse engineering allows analysts to uncover hidden functionalities within the code that may not be apparent through static or dynamic analysis alone. This level of detail is crucial for understanding complex behaviors such as encryption algorithms used by ransomware or obfuscation techniques employed by advanced persistent threats (APTs) to evade detection.
Identifying Vulnerabilities and Informing Defense Strategies
Moreover, reverse engineering can also aid in identifying vulnerabilities within the malware itself that could be exploited for defensive purposes. For instance, if an analyst discovers that a particular strain of malware relies on weak encryption methods, they may be able to develop countermeasures that exploit this weakness to neutralize the threat effectively. Additionally, reverse engineering provides valuable insights into how threat actors operate and evolve their tactics over time, enabling organizations to stay one step ahead in their defense strategies.
Advanced Malware Analysis
As cyber threats become increasingly sophisticated, advanced malware analysis techniques have emerged to address these challenges effectively. One such technique involves behavioral analysis using machine learning algorithms that can identify patterns in large datasets generated during dynamic analysis sessions. By training models on known malicious behaviors, analysts can automate parts of the detection process and improve response times when new threats emerge.
Another advanced technique involves network traffic analysis to monitor communications between infected systems and C2 servers. Tools like Wireshark allow analysts to capture and analyze packets transmitted over networks during an infection event. By examining this traffic, analysts can identify command-and-control patterns that may indicate ongoing attacks or data exfiltration attempts.
This information is crucial for developing proactive defense strategies that can mitigate threats before they escalate. Furthermore, threat intelligence sharing has become an integral part of advanced malware analysis efforts. Organizations are increasingly collaborating with one another and sharing insights about emerging threats through platforms like Information Sharing and Analysis Centers (ISACs).
By pooling resources and knowledge about specific malware strains or attack vectors, organizations can enhance their collective defenses against cyber threats.
Conclusion and Next Steps
The field of malware analysis is continually evolving as cyber threats become more complex and pervasive. As organizations strive to protect their digital assets from malicious software attacks, investing in robust malware analysis capabilities is essential. Analysts must stay informed about emerging trends in both malware development and defensive strategies to effectively combat these threats.
For those looking to deepen their expertise in malware analysis, pursuing formal education or certifications in cybersecurity can provide valuable foundational knowledge. Additionally, engaging with online communities focused on cybersecurity research can offer opportunities for collaboration and knowledge sharing among peers in the field. As technology continues to advance, so too will the methods employed by cybercriminals; therefore, ongoing education and adaptation will be key components in staying ahead in the fight against malware.
If you are interested in learning more about malware analysis, you may want to check out the article “Hello World” on Hellread.com. This article provides a beginner’s guide to programming and can be a helpful resource for those looking to enhance their skills in cybersecurity. For more advanced techniques and strategies, be sure to pick up a copy of “Mastering Malware Analysis” by Alexey Kleymenov and Amr Thabet. This comprehensive guide covers everything from setting up a malware analysis lab to reverse engineering malicious code. Click here to read the article.
FAQs
What is malware analysis?
Malware analysis is the process of examining, identifying, and understanding the behavior and purpose of a piece of malicious software, such as viruses, worms, trojans, and ransomware.
Why is malware analysis important?
Malware analysis is important for understanding how malware operates, identifying potential threats, and developing effective strategies for preventing and mitigating malware attacks.
What are the different types of malware analysis?
There are three main types of malware analysis: static analysis, dynamic analysis, and behavioral analysis. Static analysis involves examining the code and structure of the malware without executing it. Dynamic analysis involves running the malware in a controlled environment to observe its behavior. Behavioral analysis focuses on understanding the actions and impact of the malware on a system.
What are the key steps in malware analysis?
The key steps in malware analysis include collecting and identifying the malware sample, analyzing its code and behavior, determining its capabilities and impact, and developing strategies for detection and mitigation.
What are the tools and techniques used in malware analysis?
Malware analysis involves using a variety of tools and techniques, including disassemblers, debuggers, sandbox environments, and network monitoring tools. Analysts also use techniques such as reverse engineering, code deobfuscation, and pattern recognition to understand and analyze malware.