Cryptography is the science of securing communication and information through the use of mathematical techniques. It plays a crucial role in protecting sensitive data from unauthorized access and ensuring the integrity and authenticity of information. In an age where digital communication is ubiquitous, cryptography serves as a cornerstone of cybersecurity, enabling secure transactions, private communications, and the protection of personal data.
The term itself derives from the Greek words “kryptos,” meaning hidden, and “grapho,” meaning to write, which aptly describes its primary function: to conceal information from those who are not authorized to access it. The importance of cryptography extends beyond mere secrecy; it encompasses various aspects of information security, including data integrity, authentication, and non-repudiation. Data integrity ensures that information remains unchanged during transmission, while authentication verifies the identities of the parties involved in communication.
Non-repudiation prevents either party from denying their involvement in a transaction. As technology continues to evolve, so too does the need for robust cryptographic methods to safeguard against increasingly sophisticated threats.
Key Takeaways
- Cryptography is the practice and study of techniques for secure communication in the presence of third parties.
- The history of cryptography dates back to ancient times and has evolved significantly with the advancement of technology.
- The principles of cryptography include confidentiality, integrity, authentication, and non-repudiation.
- Cryptographic algorithms and protocols are used to secure data and communications, such as AES, RSA, and SSL/TLS.
- Cryptanalysis and attacks are methods used to break cryptographic systems and compromise security.
History and Evolution of Cryptography
The history of cryptography can be traced back thousands of years, with some of the earliest known examples found in ancient Egypt, where hieroglyphics were used to encode messages. The Greeks further advanced the field with the development of the Caesar cipher, named after Julius Caesar, who reportedly used it to communicate with his generals. This simple substitution cipher shifted letters in the alphabet by a fixed number, demonstrating the fundamental principle of encryption: transforming readable text into an unreadable format.
As civilizations progressed, so did cryptographic techniques. During the Middle Ages, the Arab mathematician Al-Kindi introduced frequency analysis, a method that exploits the frequency of letters in a given language to break ciphers. This marked a significant turning point in cryptography, as it highlighted the need for more complex encryption methods.
The Renaissance saw the emergence of polyalphabetic ciphers, such as the Vigenère cipher, which utilized multiple substitution alphabets to enhance security.
Principles of Cryptography
At its core, cryptography is built upon several fundamental principles that govern its operation and effectiveness. One of these principles is confidentiality, which ensures that only authorized parties can access sensitive information. This is typically achieved through encryption algorithms that transform plaintext into ciphertext, rendering it unreadable without the appropriate decryption key.
The strength of an encryption method often hinges on the complexity of its algorithm and the length of its keys. Another critical principle is integrity, which guarantees that data remains unaltered during transmission. Techniques such as hash functions are employed to create a unique digital fingerprint of data.
If even a single bit of information changes, the hash will differ significantly, alerting recipients to potential tampering. Authentication is also vital; it verifies that the parties involved in communication are who they claim to be. This is often accomplished through digital signatures or certificates issued by trusted authorities.
Lastly, non-repudiation ensures that once a transaction has occurred, neither party can deny their involvement, providing legal assurance in digital communications.
Cryptographic Algorithms and Protocols
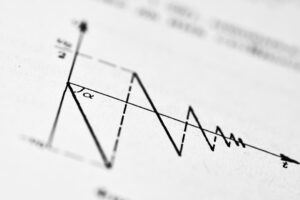
Cryptographic algorithms can be broadly categorized into two types: symmetric and asymmetric encryption. Symmetric encryption uses a single key for both encryption and decryption processes. This method is efficient and fast but poses challenges regarding key distribution; if the key is intercepted during transmission, an attacker can easily decrypt the data.
Popular symmetric algorithms include Advanced Encryption Standard (AES) and Data Encryption Standard (DES), both widely used for securing data at rest and in transit. In contrast, asymmetric encryption employs a pair of keys: a public key for encryption and a private key for decryption. This approach mitigates key distribution issues since the public key can be shared openly without compromising security.
RSA (Rivest-Shamir-Adleman) is one of the most well-known asymmetric algorithms, widely used for secure data transmission over the internet. Cryptographic protocols such as SSL/TLS (Secure Sockets Layer/Transport Layer Security) leverage these algorithms to establish secure connections between clients and servers, ensuring that data exchanged over networks remains confidential and tamper-proof.
Cryptanalysis and Attacks
Cryptanalysis is the art and science of breaking cryptographic codes and ciphers. It involves analyzing encrypted data to uncover hidden information without access to the decryption key. Various techniques are employed in cryptanalysis, including brute-force attacks, where an attacker systematically tries every possible key until finding the correct one.
While this method can be effective against weak encryption algorithms with short key lengths, modern cryptographic systems utilize significantly longer keys to thwart such attempts. Another common form of attack is known as a man-in-the-middle (MitM) attack, where an adversary intercepts communication between two parties without their knowledge. By positioning themselves between the sender and receiver, attackers can eavesdrop on conversations or even alter messages before they reach their intended destination.
To counteract these threats, cryptographic systems must continuously evolve, incorporating advanced techniques such as digital signatures and public key infrastructure (PKI) to enhance security and protect against unauthorized access.
Network Security

Protecting Data in Transit
Cryptography plays a vital role in network security by providing mechanisms to secure data packets as they traverse various network paths. This ensures that sensitive information remains confidential and protected from cyber threats.
Virtual Private Networks (VPNs)
VPNs are a prime example of how cryptography enhances network security. By creating secure tunnels for data transmission over public networks, VPNs ensure that data packets are encrypted before they leave a user’s device and decrypted upon arrival at their destination. This guarantees that sensitive information remains confidential, even when transmitted over unsecured channels like Wi-Fi networks.
Securing Network Protocols
Network protocols, such as IPsec (Internet Protocol Security), utilize cryptographic methods to secure Internet Protocol communications. This is achieved by authenticating and encrypting each IP packet in a communication session, providing an additional layer of security to network transmissions.
Secure Communication Protocols
Secure communication protocols are essential for establishing safe channels for data exchange over networks. These protocols leverage cryptographic techniques to ensure confidentiality, integrity, and authenticity during communication sessions. One of the most widely recognized secure communication protocols is HTTPS (Hypertext Transfer Protocol Secure), which combines HTTP with SSL/TLS to encrypt data exchanged between web browsers and servers.
When users access websites using HTTPS, their browsers initiate a handshake process with the server to establish a secure connection. During this process, cryptographic keys are exchanged, allowing both parties to encrypt and decrypt messages securely. This not only protects sensitive information such as login credentials and payment details but also instills trust in users by verifying the authenticity of websites through digital certificates issued by trusted certificate authorities (CAs).
Other secure communication protocols include S/MIME (Secure/Multipurpose Internet Mail Extensions) for email security and SSH (Secure Shell) for secure remote access to servers.
Future Trends in Cryptography and Network Security
As technology continues to advance at an unprecedented pace, so too do the challenges facing cryptography and network security. One significant trend is the rise of quantum computing, which poses potential threats to traditional cryptographic algorithms. Quantum computers have the capability to solve complex mathematical problems much faster than classical computers, potentially rendering many current encryption methods obsolete.
In response, researchers are actively exploring post-quantum cryptography—new algorithms designed to withstand attacks from quantum computers. Another emerging trend is the increasing emphasis on privacy-preserving technologies such as homomorphic encryption and zero-knowledge proofs. These techniques allow computations to be performed on encrypted data without revealing sensitive information, enabling secure data sharing while maintaining privacy.
Additionally, as cyber threats become more sophisticated, organizations are adopting more comprehensive security frameworks that integrate machine learning and artificial intelligence into their cybersecurity strategies. These technologies can enhance threat detection capabilities by analyzing vast amounts of data in real-time to identify anomalies indicative of potential attacks. In conclusion, cryptography remains an essential field within cybersecurity that continues to evolve alongside technological advancements and emerging threats.
Its principles underpin secure communication protocols and network security measures that protect sensitive information in an increasingly interconnected world. As we look toward the future, ongoing research and innovation will be critical in developing robust solutions that address new challenges while ensuring the confidentiality, integrity, and authenticity of digital communications.
If you are interested in learning more about cryptography and network security, you may also want to check out the article “Hello World” on Hellread.com. This article discusses the basics of programming and how it relates to cybersecurity. You can read it here.
FAQs
What is cryptography?
Cryptography is the practice and study of techniques for secure communication in the presence of third parties. It involves creating and analyzing protocols that prevent third parties or the public from reading private messages.
What is network security?
Network security is the practice of securing a computer network infrastructure against unauthorized access, misuse, malfunction, modification, destruction, or improper disclosure.
Who is William Stallings?
William Stallings is a well-known author in the field of computer science and engineering. He has written numerous books on topics such as computer organization and architecture, operating systems, and network security.
What are the main goals of cryptography and network security?
The main goals of cryptography and network security are to ensure the confidentiality, integrity, and availability of data and resources within a computer network. This includes protecting against unauthorized access, data tampering, and denial of service attacks.
What are some common cryptographic techniques?
Common cryptographic techniques include encryption, hashing, digital signatures, and public key infrastructure (PKI). These techniques are used to secure data and communications in various applications, such as online banking, e-commerce, and secure messaging.
What are some common network security measures?
Common network security measures include firewalls, intrusion detection systems, virtual private networks (VPNs), and access control mechanisms. These measures help to protect a network from unauthorized access and malicious activities.