The realm of networking is vast and intricate, with routing and switching serving as foundational pillars that support the entire infrastructure. The “Packet Guide to Routing and Switching” is an essential resource for network professionals, providing a comprehensive overview of the principles and practices that govern these critical functions. This guide delves into the mechanisms that enable data to traverse networks efficiently, ensuring that information reaches its intended destination with speed and accuracy.
As organizations increasingly rely on robust networking solutions to facilitate communication and data exchange, understanding the nuances of routing and switching becomes paramount. In this guide, readers will encounter a blend of theoretical concepts and practical applications, making it suitable for both novices and seasoned professionals. The text covers a wide array of topics, from basic definitions to advanced configurations, ensuring that it caters to a diverse audience.
By exploring the intricacies of routing protocols, switching technologies, and network design principles, the guide equips readers with the knowledge necessary to navigate the complexities of modern networking environments. As we embark on this exploration, it is crucial to grasp the fundamental concepts that underpin routing and switching, as they form the backbone of effective network communication.
Key Takeaways
- Packet Guide to Routing and Switching provides a comprehensive overview of networking concepts and technologies.
- Understanding the basics of routing and switching is essential for building and maintaining a reliable network infrastructure.
- Configuring routers and switches involves setting up IP addresses, routing protocols, and VLANs to ensure proper network functionality.
- Troubleshooting routing and switching issues requires a systematic approach to identify and resolve connectivity and performance problems.
- Implementing security measures in routing and switching is crucial for protecting sensitive data and preventing unauthorized access to the network.
Understanding Routing and Switching Concepts
At its core, routing refers to the process of determining the optimal path for data packets to travel across a network. Routers play a pivotal role in this process by analyzing incoming data packets and making decisions based on their destination addresses. This decision-making process involves various routing protocols, such as RIP (Routing Information Protocol), OSPF (Open Shortest Path First), and BGP (Border Gateway Protocol), each with its unique characteristics and use cases.
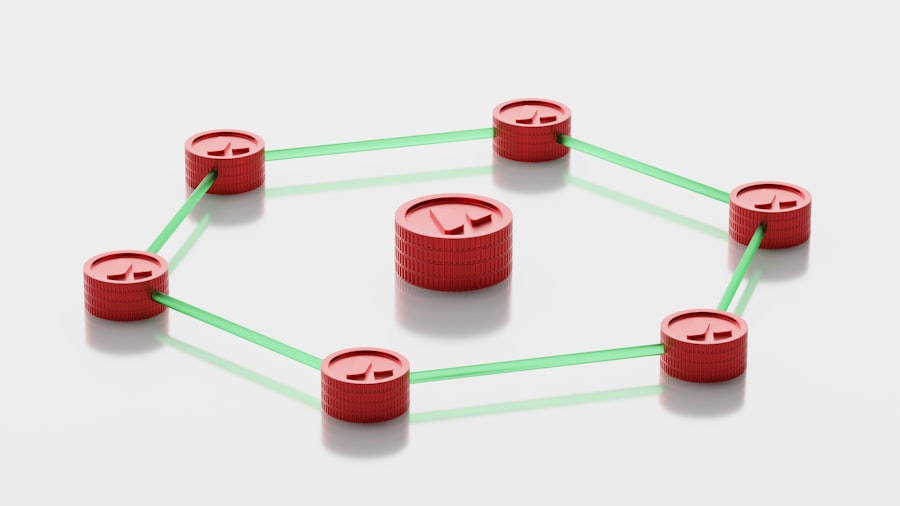
For instance, OSPF is often favored in larger enterprise networks due to its ability to efficiently manage complex topologies through link-state routing. Switching, on the other hand, operates at a different layer of the OSI model, primarily focusing on local area networks (LANs). Switches facilitate communication between devices within the same network by forwarding data frames based on MAC (Media Access Control) addresses.
Unlike routers, which operate at Layer 3 (Network Layer), switches function at Layer 2 (Data Link Layer). This distinction is crucial as it highlights the different roles these devices play in network architecture. For example, a switch can significantly reduce network congestion by creating separate collision domains for each connected device, thereby enhancing overall performance.
The interplay between routing and switching is essential for creating efficient networks.
Understanding how these two functions complement each other allows network engineers to design systems that optimize performance and reliability.
Moreover, as networks evolve with the advent of technologies like software-defined networking (SDN) and network function virtualization (NFV), the lines between routing and switching continue to blur, necessitating a deeper understanding of both domains.
Configuring Routers and Switches
Configuring routers and switches is a critical skill for network administrators, as it directly impacts the performance and security of the network. The configuration process typically begins with accessing the device’s command-line interface (CLI), where administrators can input commands to set up various parameters. For routers, this may involve configuring interfaces, setting up routing protocols, and establishing access control lists (ACLs) to manage traffic flow.
For instance, enabling OSPF on a router requires specifying router IDs, defining network statements, and adjusting timers to optimize convergence times. Switch configuration often focuses on VLAN (Virtual Local Area Network) setup, port assignments, and spanning tree protocol (STP) settings. VLANs allow network administrators to segment traffic logically, improving security and reducing broadcast domains.
For example, by creating separate VLANs for different departments within an organization, administrators can ensure that sensitive data remains isolated from general traffic. Additionally, configuring STP helps prevent loops in the network topology, which can lead to broadcast storms and degraded performance. Beyond basic configurations, advanced features such as Quality of Service (QoS) settings can be implemented to prioritize certain types of traffic over others.
This is particularly important in environments where bandwidth is limited or where specific applications require low latency, such as VoIP or video conferencing. By understanding how to configure routers and switches effectively, network professionals can create resilient infrastructures that meet the demands of modern applications while maintaining high levels of performance.
Troubleshooting Routing and Switching Issues
Troubleshooting routing and switching issues is an inevitable part of managing a network. When problems arise—such as connectivity issues or slow performance—network administrators must employ systematic approaches to identify and resolve these challenges. One effective method is the use of the OSI model as a framework for troubleshooting.
By isolating issues at specific layers of the model, administrators can narrow down potential causes more efficiently. For example, if users are unable to access a website, checking Layer 1 (Physical Layer) for cable connections or Layer 2 (Data Link Layer) for switch configurations can help pinpoint the issue. Common tools used in troubleshooting include ping tests, traceroute commands, and network analyzers like Wireshark.
A ping test can quickly determine if a device is reachable over the network by sending ICMP echo requests. If packets are lost or delayed, further investigation into routing tables or switch configurations may be warranted. Traceroute provides insight into the path packets take through the network, revealing any potential bottlenecks or misconfigured routers along the way.
In addition to these tools, maintaining comprehensive documentation of network configurations is vital for effective troubleshooting. This documentation should include details about device settings, IP address assignments, and any changes made over time. When issues arise, having access to this information allows administrators to quickly revert configurations or identify discrepancies that may be causing problems.
Ultimately, a proactive approach to troubleshooting—combined with a solid understanding of routing and switching principles—enables network professionals to maintain optimal performance and reliability in their environments.
Implementing Security Measures in Routing and Switching
As networks become increasingly complex and interconnected, implementing robust security measures in routing and switching is essential to protect sensitive data from unauthorized access and cyber threats. One fundamental aspect of securing routers is configuring strong passwords and enabling encryption protocols such as SSH (Secure Shell) for remote management access. This prevents unauthorized users from gaining control over critical devices that could compromise the entire network.
Access control lists (ACLs) are another vital security feature that can be implemented on both routers and switches. ACLs allow administrators to define rules that specify which traffic is permitted or denied based on IP addresses or protocols. For instance, an organization may choose to block all incoming traffic from specific IP ranges known for malicious activity while allowing legitimate traffic through designated ports.
This granular control helps mitigate risks associated with external threats while ensuring that internal communications remain uninterrupted. In addition to these measures, implementing features such as port security on switches can further enhance network security. Port security allows administrators to restrict access to specific MAC addresses on switch ports, preventing unauthorized devices from connecting to the network.
If an unauthorized device attempts to connect, the switch can automatically disable the port or send alerts to administrators for further investigation. By combining these security practices with regular audits and updates to firmware and software, organizations can create a resilient defense against evolving cyber threats in their routing and switching environments.
Advanced Routing and Switching Techniques
As networking technology continues to evolve, advanced routing and switching techniques have emerged that enhance performance and scalability in complex environments. One such technique is route redistribution, which allows different routing protocols to share information with one another. This is particularly useful in hybrid networks where multiple protocols are in use; for example, redistributing routes between OSPF and EIGRP (Enhanced Interior Gateway Routing Protocol) enables seamless communication across diverse segments of the network.
Another advanced technique is link aggregation, which combines multiple physical links into a single logical link to increase bandwidth and provide redundancy. This approach not only enhances throughput but also improves fault tolerance; if one link fails, traffic can continue flowing through the remaining links without interruption. Link aggregation is commonly implemented in high-traffic environments such as data centers or enterprise networks where maximizing bandwidth is critical.
Additionally, technologies like MPLS (Multiprotocol Label Switching) have gained traction for their ability to optimize traffic flow across wide area networks (WANs). MPLS uses labels instead of traditional IP addresses to make forwarding decisions at routers, allowing for faster packet processing and improved quality of service for applications requiring low latency. By leveraging these advanced techniques, network engineers can design infrastructures that are not only efficient but also capable of adapting to future demands.
Best Practices for Routing and Switching
Adhering to best practices in routing and switching is essential for maintaining a reliable and efficient network infrastructure. One fundamental practice is implementing hierarchical network design principles. This approach involves structuring networks into distinct layers—core, distribution, and access—each serving specific functions.
The core layer focuses on high-speed data transport between different parts of the network; the distribution layer manages policy-based connectivity; while the access layer connects end-user devices directly to the network. Regularly updating device firmware and software is another critical best practice that cannot be overlooked. Keeping devices up-to-date ensures that they are equipped with the latest security patches and performance enhancements.
Network administrators should establish a routine schedule for updates while also monitoring vendor announcements for critical patches that may need immediate attention. Documentation plays a vital role in effective routing and switching management as well. Comprehensive records of configurations, changes made over time, and network diagrams help streamline troubleshooting efforts while providing clarity during audits or assessments.
Furthermore, conducting regular training sessions for staff ensures that team members remain informed about new technologies and best practices in networking.
Future Trends in Routing and Switching Technology
The future of routing and switching technology promises exciting advancements driven by emerging trends such as automation, artificial intelligence (AI), and increased adoption of cloud services. Automation tools are becoming increasingly prevalent in managing complex networks by enabling automated configuration changes based on predefined policies or real-time analytics. This shift not only reduces human error but also enhances operational efficiency by allowing administrators to focus on strategic initiatives rather than routine tasks.
AI-driven analytics are also transforming how networks are monitored and managed. By leveraging machine learning algorithms, organizations can gain insights into traffic patterns, detect anomalies indicative of potential security threats or performance issues before they escalate into significant problems. This proactive approach empowers network teams to respond swiftly while minimizing downtime.
Moreover, as organizations continue migrating towards cloud-based solutions, hybrid cloud architectures are becoming more common. This trend necessitates advanced routing techniques capable of seamlessly integrating on-premises resources with cloud services while ensuring optimal performance across diverse environments. Technologies such as SD-WAN (Software-Defined Wide Area Networking) are gaining traction as they provide flexible connectivity options tailored for cloud applications while enhancing security through centralized management.
In summary, as we look ahead at routing and switching technology’s trajectory over the coming years—marked by automation advancements alongside increased reliance on cloud services—it becomes clear that staying abreast of these trends will be crucial for networking professionals aiming to build resilient infrastructures capable of meeting future demands.
If you are interested in learning more about networking and technology, you may also enjoy reading the article “Hello World” on Hellread.com. This article discusses the basics of programming and computer science, which can be helpful in understanding the concepts presented in Bruce Hartpence’s Packet Guide to Routing and Switching. Check it out here.
FAQs
What is routing and switching?
Routing and switching are two fundamental functions of network communication. Routing involves directing data packets from one network to another, while switching involves forwarding data within a single network.
What is the purpose of routing and switching?
The purpose of routing and switching is to ensure that data packets are efficiently and accurately delivered to their intended destinations within a network or across multiple networks.
What are some common routing protocols?
Common routing protocols include RIP (Routing Information Protocol), OSPF (Open Shortest Path First), EIGRP (Enhanced Interior Gateway Routing Protocol), and BGP (Border Gateway Protocol).
What are some common switching technologies?
Common switching technologies include Ethernet, VLANs (Virtual Local Area Networks), and STP (Spanning Tree Protocol).
What are some key concepts in routing and switching?
Key concepts in routing and switching include IP addressing, subnetting, routing tables, switching fabric, and network topologies.
What are some best practices for routing and switching?
Best practices for routing and switching include proper network design, security measures, redundancy, and regular maintenance and monitoring of network devices.