The Network+ Guide to Networks serves as a foundational text for individuals seeking to understand the complexities of networking. This guide is particularly valuable for those preparing for the CompTIA Network+ certification, which is recognized globally as a benchmark for networking proficiency. The guide delves into various aspects of networking, including the principles of network design, implementation, and management.
It is structured to cater to both novices and seasoned professionals, providing a comprehensive overview of essential networking concepts and practices. In an era where connectivity is paramount, understanding networks is not merely an academic pursuit; it is a necessity for anyone involved in information technology. The Network+ Guide to Networks equips readers with the knowledge required to navigate the intricacies of modern networking environments.
From basic concepts such as IP addressing and subnetting to more advanced topics like network security and virtualization, this guide serves as a roadmap for mastering the skills needed in today’s digital landscape.
Key Takeaways
- Network+ Guide to Networks provides a comprehensive overview of networking concepts and technologies.
- Understanding Network Basics covers the fundamental principles of networking, including protocols, topologies, and network models.
- Exploring Network Hardware delves into the various components and devices used in networking, such as routers, switches, and cables.
- Configuring and Managing Network Devices discusses the process of setting up and maintaining network devices, including IP addressing and device management.
- Network Security and Troubleshooting addresses the importance of network security measures and provides guidance on identifying and resolving common network issues.
Understanding Network Basics
The OSI Model: A Framework for Network Communication
The OSI (Open Systems Interconnection) model is a key framework that outlines the layers involved in network communication. It consists of seven layers, each serving a specific function, from physical transmission of data to application-level interactions. The first layer, the Physical layer, deals with the actual hardware and transmission media used to send data. This includes cables, switches, and network interface cards (NICs). The Data Link layer follows, ensuring that data packets are correctly formatted for transmission over the physical medium. As one progresses through the layers, each subsequent layer adds complexity and functionality, culminating in the Application layer, where end-user applications interact with the network.
Understanding the OSI Model and Its Importance
Understanding this model helps network professionals diagnose issues and design efficient networks.
IP Addressing: A Critical Aspect of Network Basics
Another critical aspect of network basics is the concept of IP addressing. Every device on a network requires a unique identifier known as an IP address to communicate effectively. IPv4 and IPv6 are the two primary versions of IP addressing currently in use. IPv4 addresses are 32-bit numbers typically represented in decimal format, while IPv6 addresses are 128-bit numbers expressed in hexadecimal. The transition from IPv4 to IPv6 is significant due to the increasing number of devices connected to the internet, necessitating a more extensive addressing scheme.
Exploring Network Hardware

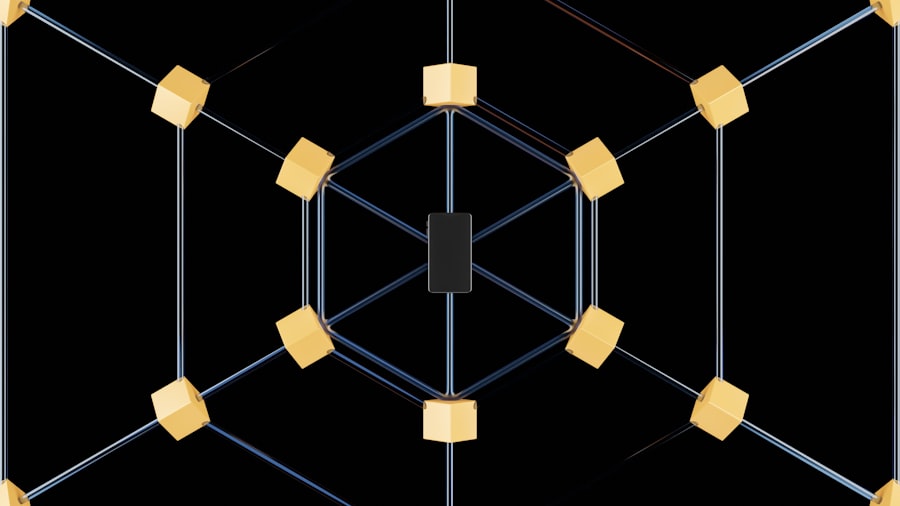
Network hardware forms the backbone of any networking infrastructure. Various devices play distinct roles in facilitating communication between endpoints. Routers, switches, hubs, and access points are among the most common hardware components found in networks today.
Each device has its specific function; for instance, routers connect different networks and direct data packets between them, while switches operate within a single network to connect devices and manage data traffic efficiently. Switches are particularly important in local area networks (LANs), where they create a network by connecting multiple devices within a limited geographical area. Unlike hubs, which broadcast data to all connected devices, switches intelligently forward data only to the intended recipient based on MAC addresses.
This capability enhances network performance and security by reducing unnecessary traffic. Additionally, managed switches offer advanced features such as VLAN support and traffic monitoring, allowing network administrators to optimize performance further. Routers serve as gateways between different networks, such as connecting a home or office network to the internet.
They perform critical functions such as packet forwarding and routing based on IP addresses. Modern routers often come equipped with additional features like firewall capabilities and Quality of Service (QoS) settings that prioritize certain types of traffic over others. Understanding how these devices work together is essential for designing robust and efficient networks.
Configuring and Managing Network Devices
Configuring network devices is a vital skill for any networking professional. Proper configuration ensures that devices operate optimally and securely within a network environment. This process often begins with accessing the device’s management interface, which can be done through command-line interfaces (CLI) or graphical user interfaces (GUI).
Familiarity with these interfaces allows administrators to set parameters such as IP addresses, subnet masks, and routing protocols. For instance, configuring a router typically involves setting up interfaces with appropriate IP addresses and enabling routing protocols like RIP (Routing Information Protocol) or OSPF (Open Shortest Path First). These protocols help routers communicate with one another and determine the best paths for data transmission across complex networks.
Additionally, security settings such as access control lists (ACLs) can be implemented to restrict unauthorized access to sensitive areas of the network. Network management extends beyond initial configuration; it also involves ongoing monitoring and maintenance. Tools such as SNMP (Simple Network Management Protocol) allow administrators to monitor device performance and receive alerts about potential issues before they escalate into significant problems.
Regular updates and patches are also crucial for maintaining device security and functionality. By staying proactive in managing network devices, IT professionals can ensure that their networks remain reliable and secure.
Network Security and Troubleshooting
Network security is an increasingly critical concern in today’s interconnected world. With cyber threats evolving constantly, organizations must implement robust security measures to protect their data and infrastructure. Fundamental concepts in network security include firewalls, intrusion detection systems (IDS), and encryption protocols.
Firewalls act as barriers between trusted internal networks and untrusted external networks, filtering incoming and outgoing traffic based on predefined security rules. Intrusion detection systems monitor network traffic for suspicious activity and can alert administrators to potential breaches in real-time. Encryption protocols such as SSL/TLS ensure that data transmitted over networks remains confidential and secure from eavesdropping or tampering.
Understanding these security measures is essential for safeguarding sensitive information and maintaining compliance with regulations such as GDPR or HIPAA. Troubleshooting is another critical aspect of network management that requires a systematic approach. When issues arise within a network, identifying the root cause can be challenging due to the interconnected nature of devices and services.
A common troubleshooting methodology involves defining the problem, gathering information about the network environment, testing hypotheses, and implementing solutions. Tools such as ping tests, traceroute commands, and network analyzers can assist in diagnosing connectivity issues or performance bottlenecks. For example, if users report slow internet speeds, an administrator might start by checking bandwidth usage across the network using monitoring tools.
If excessive usage is detected from a particular device or application, steps can be taken to limit its impact on overall performance. By employing effective troubleshooting techniques, network professionals can minimize downtime and ensure that users have reliable access to resources.
Wireless Networking
Wireless Networking Standards
The most common standard for wireless networking is IEEE 802.
11a/b/g/n/ac/ax. Each iteration has brought improvements in speed, range, and capacity. For instance, 802.11ac introduced multi-user MIMO (MU-MIMO) technology that allows multiple devices to communicate simultaneously with a single access point, significantly enhancing performance in environments with many connected devices.
Security Challenges
However, wireless networking also presents unique challenges related to security. Securing wireless networks requires implementing strong encryption protocols like WPA3 (Wi-Fi Protected Access 3) to protect against unauthorized access.
Optimizing Wireless Coverage
Additionally, understanding how physical obstacles like walls or electronic interference from other devices can affect signal strength is crucial for optimizing wireless coverage in an environment.
Virtualization and Cloud Computing
Virtualization has transformed how organizations deploy and manage their IT resources by allowing multiple virtual machines (VMs) to run on a single physical server. This technology enables more efficient use of hardware resources while providing flexibility in resource allocation based on demand. Hypervisors like VMware ESXi or Microsoft Hyper-V facilitate this process by creating an abstraction layer between physical hardware and virtual machines.
Cloud computing takes virtualization a step further by delivering computing resources over the internet on an as-needed basis. Services such as Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS) allow organizations to scale their operations without investing heavily in physical infrastructure. For example, Amazon Web Services (AWS) provides scalable cloud solutions that enable businesses to deploy applications quickly without worrying about underlying hardware constraints.
The integration of virtualization and cloud computing has also led to new networking paradigms such as Software-Defined Networking (SDN). SDN separates the control plane from the data plane in networking devices, allowing for centralized management of network resources through software applications. This approach enhances agility and simplifies network management by enabling administrators to programmatically adjust network configurations based on real-time needs.
Advanced Networking Technologies
As technology continues to evolve rapidly, advanced networking technologies are emerging that promise to reshape how we connect and communicate. One such technology is 5G wireless communication, which offers significantly higher speeds and lower latency compared to previous generations of mobile networks. This advancement opens up new possibilities for applications such as IoT (Internet of Things), autonomous vehicles, and smart cities.
Another notable development is the rise of edge computing, which brings computation closer to data sources rather than relying solely on centralized cloud servers. By processing data at the edge of the network—near where it is generated—organizations can reduce latency and improve response times for applications requiring real-time processing. Additionally, advancements in artificial intelligence (AI) are being integrated into networking technologies for enhanced automation and predictive analytics.
AI-driven tools can analyze vast amounts of network data to identify patterns or anomalies that may indicate potential issues or security threats before they escalate into significant problems. These advanced technologies not only enhance connectivity but also introduce new challenges related to security, management, and interoperability that networking professionals must navigate effectively. As organizations continue to adopt these innovations, staying informed about emerging trends will be crucial for success in the ever-evolving field of networking.
If you are interested in expanding your knowledge on networking, you may want to check out an article on Hellread titled “Hello World.” This article provides insights into the basics of networking and can complement the information found in the Network+ Guide to Networks by Jill West, Tamara Dean, and Jean Andrews. You can read the article here.
FAQs
What is the Network+ Guide to Networks about?
The Network+ Guide to Networks is a comprehensive guide to networking concepts, technologies, and practices. It covers a wide range of topics including network design, implementation, management, and security.
Who are the authors of the Network+ Guide to Networks?
The Network+ Guide to Networks is authored by Jill West, Tamara Dean, and Jean Andrews. They are experienced educators and professionals in the field of networking and have written several books on the subject.
What topics are covered in the Network+ Guide to Networks?
The Network+ Guide to Networks covers a wide range of topics including networking fundamentals, network design and implementation, network protocols, network security, and network management. It also includes hands-on exercises and case studies to reinforce the concepts.
Is the Network+ Guide to Networks suitable for beginners?
Yes, the Network+ Guide to Networks is suitable for beginners as it provides a comprehensive introduction to networking concepts and technologies. It is written in a clear and accessible manner, making it easy for beginners to understand and learn from.
Is the Network+ Guide to Networks up to date with the latest networking technologies?
Yes, the Network+ Guide to Networks is regularly updated to include the latest networking technologies and practices. It covers topics such as cloud computing, virtualization, and mobile networking to ensure that readers are informed about the latest developments in the field.