Applied cryptography is a critical field that encompasses the practical implementation of cryptographic techniques to secure communication and protect sensitive information. As the digital landscape continues to evolve, the need for robust security measures has become paramount. The proliferation of the internet, mobile devices, and cloud computing has created an environment where data breaches and cyber threats are increasingly common.
In this context, applied cryptography serves as a cornerstone of information security, providing the tools and methodologies necessary to safeguard data from unauthorized access and manipulation. The significance of applied cryptography extends beyond mere data protection; it plays a vital role in establishing trust in digital interactions. Whether it is securing online transactions, protecting personal information, or ensuring the integrity of communications, cryptographic techniques are employed to create a secure framework for digital exchanges.
This article delves into the fundamental principles of cryptography, explores various algorithms and protocols, examines real-world applications, and discusses the challenges posed by cryptographic attacks, all while highlighting the indispensable role of applied cryptography in contemporary information security.
Key Takeaways
- Applied cryptography is the practice of using cryptographic techniques to secure communication and protect sensitive information.
- The basics of cryptography involve understanding concepts such as encryption, decryption, and key management.
- Cryptographic algorithms and protocols are the building blocks of secure communication, including symmetric and asymmetric encryption, digital signatures, and secure key exchange.
- Cryptographic applications in the real world include secure messaging, online banking, and digital signatures for legal documents.
- Understanding cryptographic attacks and defenses is crucial for maintaining the security of encrypted communication and data.
The Basics of Cryptography
Types of Encryption
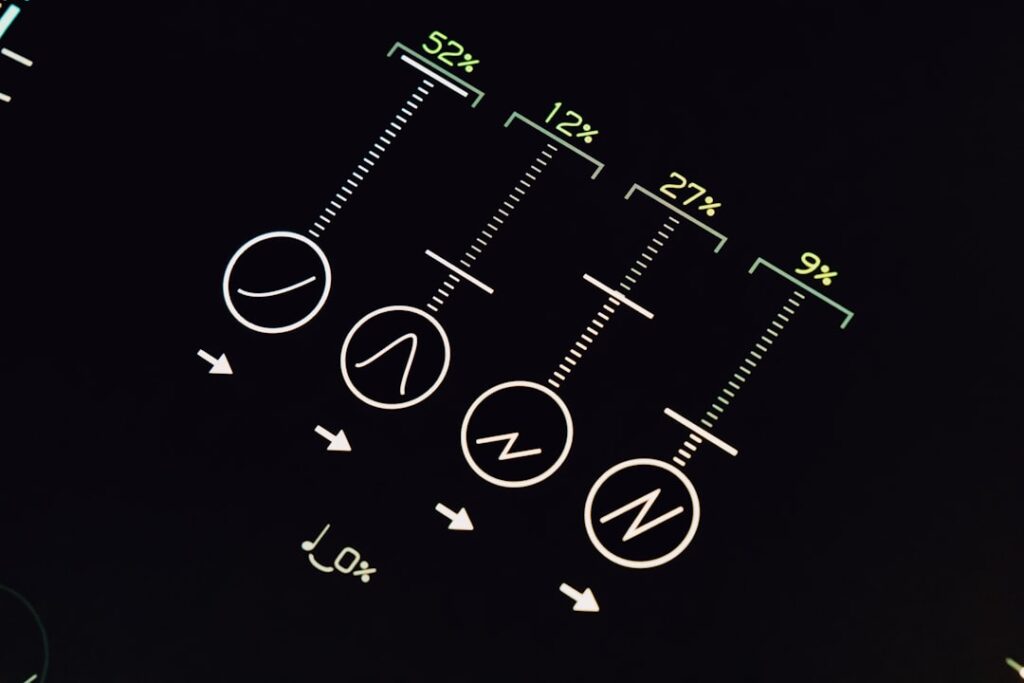
In contemporary practice, cryptography is categorized into two primary types: symmetric and asymmetric encryption. Symmetric encryption involves a single key for both encryption and decryption, making it efficient for large volumes of data. However, the challenge lies in securely sharing the key between parties.
Asymmetric Encryption
Asymmetric encryption, on the other hand, utilizes a pair of keys: a public key for encryption and a private key for decryption. This method addresses the key distribution problem inherent in symmetric encryption, allowing users to share their public keys openly while keeping their private keys confidential.
Foundational Concepts and Applications
The RSA algorithm is one of the most well-known asymmetric encryption methods, relying on the mathematical properties of prime numbers to ensure security. Understanding these foundational concepts is essential for grasping the complexities of applied cryptography and its various applications in securing digital communications.
Cryptographic Algorithms and Protocols

Cryptographic algorithms are the mathematical functions that underpin encryption and decryption processes. They are designed to transform plaintext into ciphertext, rendering it unreadable to unauthorized users. Among the most widely used symmetric algorithms are Advanced Encryption Standard (AES) and Data Encryption Standard (DES).
AES, adopted by the U.S. government in 2001, is known for its efficiency and security, utilizing key sizes of 128, 192, or 256 bits to provide varying levels of protection. DES, while historically significant, has largely been phased out due to its vulnerability to brute-force attacks.
In addition to symmetric algorithms, various protocols leverage cryptographic techniques to facilitate secure communication over networks. The Transport Layer Security (TLS) protocol is a prime example, providing a secure channel between web browsers and servers. TLS employs a combination of asymmetric and symmetric encryption to establish a secure connection, ensuring that data transmitted over the internet remains confidential and tamper-proof.
Another notable protocol is Pretty Good Privacy (PGP), which is widely used for securing emails through a combination of hashing, compression, and encryption techniques. These algorithms and protocols form the backbone of modern cryptographic practices, enabling secure transactions and communications across diverse platforms.
Cryptographic Applications in the Real World
The applications of applied cryptography are vast and varied, permeating numerous aspects of daily life. One of the most prominent uses is in securing online transactions through e-commerce platforms. When consumers make purchases online, their payment information must be transmitted securely to prevent interception by malicious actors.
Cryptographic techniques such as SSL/TLS ensure that sensitive data like credit card numbers are encrypted during transmission, safeguarding against fraud and identity theft. Another significant application is in securing communications through messaging apps. End-to-end encryption has become a standard feature in many popular messaging platforms, such as WhatsApp and Signal.
This ensures that only the intended recipients can read the messages exchanged between users, protecting their privacy from potential eavesdroppers. Additionally, applied cryptography plays a crucial role in securing digital signatures, which authenticate the identity of individuals or organizations in electronic transactions. This is particularly important in legal contexts where verifying the authenticity of documents is essential.
Cryptographic Attacks and Defenses
Despite the robust nature of cryptographic systems, they are not impervious to attacks. Cybercriminals continuously develop sophisticated methods to exploit vulnerabilities in cryptographic algorithms and protocols. One common type of attack is known as a brute-force attack, where an attacker systematically attempts every possible key until the correct one is found.
While modern encryption standards like AES are designed to withstand such attacks due to their large key sizes, older algorithms like DES have become increasingly vulnerable as computational power has grown. Another prevalent attack vector is known as a man-in-the-middle (MitM) attack, where an adversary intercepts communication between two parties without their knowledge. This can occur when users connect to unsecured Wi-Fi networks or fail to verify digital certificates during secure connections.
To defend against such attacks, various strategies have been developed, including the use of public key infrastructure (PKI) for certificate validation and implementing multi-factor authentication (MFA) to add an additional layer of security. These defenses are essential in maintaining the integrity and confidentiality of sensitive information in an increasingly hostile cyber environment.
The Role of Applied Cryptography in Information Security
Applied cryptography serves as a foundational element in the broader field of information security.
Organizations across various sectors rely on cryptographic techniques to comply with regulatory requirements such as GDPR or HIPAA, which mandate stringent data protection measures.
By implementing robust cryptographic solutions, businesses can mitigate risks associated with data breaches and maintain customer trust. Moreover, applied cryptography plays a pivotal role in securing emerging technologies such as blockchain and Internet of Things (IoT) devices.
Each block contains a unique hash that references the previous block’s hash, creating an immutable chain that is resistant to tampering. Similarly, IoT devices often utilize lightweight cryptographic algorithms to secure communication between devices while balancing performance constraints. As technology continues to advance, the role of applied cryptography will only become more critical in safeguarding sensitive information across diverse applications.
The Future of Applied Cryptography
As we look toward the future, several trends are shaping the landscape of applied cryptography. One significant development is the rise of quantum computing, which poses potential threats to traditional cryptographic algorithms. Quantum computers have the capability to solve complex mathematical problems at unprecedented speeds, rendering many current encryption methods vulnerable to attacks.
In response to this emerging threat, researchers are actively exploring post-quantum cryptography—new algorithms designed to withstand quantum attacks while maintaining efficiency. Additionally, advancements in machine learning and artificial intelligence are influencing how cryptographic systems are designed and implemented. These technologies can enhance threat detection capabilities by analyzing patterns in data traffic and identifying anomalies that may indicate potential attacks.
Furthermore, they can assist in optimizing cryptographic algorithms for performance without compromising security. As these technologies continue to evolve, they will likely play an integral role in shaping the future landscape of applied cryptography.
The Importance of Applied Cryptography
The importance of applied cryptography cannot be overstated in today’s digital age. As cyber threats become more sophisticated and pervasive, robust cryptographic measures are essential for protecting sensitive information and maintaining trust in digital interactions. From securing online transactions to safeguarding communications through messaging apps, applied cryptography underpins countless aspects of modern life.
As we navigate an increasingly interconnected world filled with emerging technologies and evolving threats, the role of applied cryptography will only grow more critical. By understanding its principles and applications, individuals and organizations can better equip themselves to face the challenges posed by cyber adversaries while ensuring that their data remains secure and private. The ongoing advancements in this field will continue to shape our digital future, making it imperative for stakeholders across all sectors to prioritize applied cryptography as a fundamental component of their security strategies.
If you are interested in learning more about cryptography and its applications, you may want to check out the article “Hello World” on hellread.com. This article delves into the basics of cryptography and how it is used in various industries to secure sensitive information. It provides a great introduction to the topic and complements the concepts discussed in Bruce Schneier’s book “Applied Cryptography.”
FAQs
What is Applied Cryptography?
Applied cryptography is the practice of using cryptographic techniques to secure communication and protect sensitive information. It involves the application of cryptographic algorithms and protocols to real-world scenarios, such as securing data transmission over the internet or protecting personal information.
Who is Bruce Schneier?
Bruce Schneier is a renowned cryptographer, security technologist, and author. He is the author of the book “Applied Cryptography,” which is considered a seminal work in the field of cryptography. Schneier is also known for his work in security and privacy, and he is a respected voice in the cybersecurity community.
What is the book “Applied Cryptography” about?
“Applied Cryptography” is a book written by Bruce Schneier that provides a comprehensive overview of cryptographic algorithms, protocols, and techniques. The book covers a wide range of topics, including encryption, digital signatures, key management, and cryptographic protocols. It is widely regarded as a foundational text in the field of cryptography.
Why is “Applied Cryptography” important?
“Applied Cryptography” is important because it provides a thorough and accessible introduction to the principles and practices of cryptography. The book has been influential in shaping the way cryptography is used in real-world applications, and it has helped to educate and inform professionals in the field of cybersecurity.