Packet analysis is a critical component of network management and security, serving as a window into the intricate workings of data transmission across networks. At its core, packet analysis involves capturing and inspecting data packets that traverse a network, allowing network administrators and security professionals to understand the flow of information, diagnose issues, and identify potential threats. As networks become increasingly complex, with the proliferation of devices and applications, the ability to analyze packets effectively has become indispensable for maintaining optimal performance and security.
The significance of packet analysis extends beyond mere observation; it encompasses a range of activities that include monitoring traffic, troubleshooting connectivity issues, and detecting anomalies that may indicate security breaches. By examining the contents of packets, professionals can glean insights into the types of protocols in use, the volume of traffic, and the behavior of applications. This level of scrutiny is essential for ensuring that networks operate efficiently and securely, particularly in environments where sensitive data is transmitted.
As organizations continue to rely on digital communication, the demand for skilled packet analysts is likely to grow, making this an essential area of expertise in the field of information technology.
Key Takeaways
- Packet analysis is the process of capturing and analyzing data packets to understand and troubleshoot network issues.
- Tools such as Wireshark and tcpdump are commonly used for packet analysis, while techniques like filtering and decoding help in extracting useful information from packets.
- Understanding network protocols such as TCP/IP, HTTP, and DNS is crucial for effective packet analysis.
- Identifying and analyzing network traffic patterns can help in detecting anomalies and optimizing network performance.
- Packet analysis is essential for detecting and analyzing security threats, and real-world case studies can provide valuable insights into this process.
Tools and Techniques for Packet Analysis
A variety of tools and techniques are available for conducting packet analysis, each offering unique features and capabilities tailored to different needs. One of the most widely used tools is Wireshark, an open-source packet analyzer that provides a user-friendly interface for capturing and inspecting packets in real-time. Wireshark supports a multitude of protocols and allows users to filter traffic based on specific criteria, making it an invaluable resource for both novice and experienced analysts.
Its ability to dissect packets down to their individual fields enables users to understand the nuances of network communication, facilitating deeper insights into traffic behavior. In addition to Wireshark, other tools such as tcpdump and Microsoft Message Analyzer also play significant roles in packet analysis. Tcpdump is a command-line utility that captures network packets and displays them in a readable format, making it particularly useful for quick diagnostics in environments where graphical interfaces may not be available.
On the other hand, Microsoft Message Analyzer offers advanced features for analyzing network traffic and application messages, allowing users to visualize data flows and identify performance bottlenecks. Each tool has its strengths, and the choice often depends on the specific requirements of the analysis being conducted. Techniques for packet analysis can vary widely based on the objectives of the analysis.
For instance, passive analysis involves monitoring traffic without altering it, which is crucial for understanding normal network behavior. In contrast, active analysis may involve injecting packets into the network to test responses or simulate attacks. Additionally, deep packet inspection (DPI) allows analysts to examine the payload of packets beyond just header information, providing insights into application-level data that can be critical for identifying security threats or performance issues.
Understanding Network Protocols
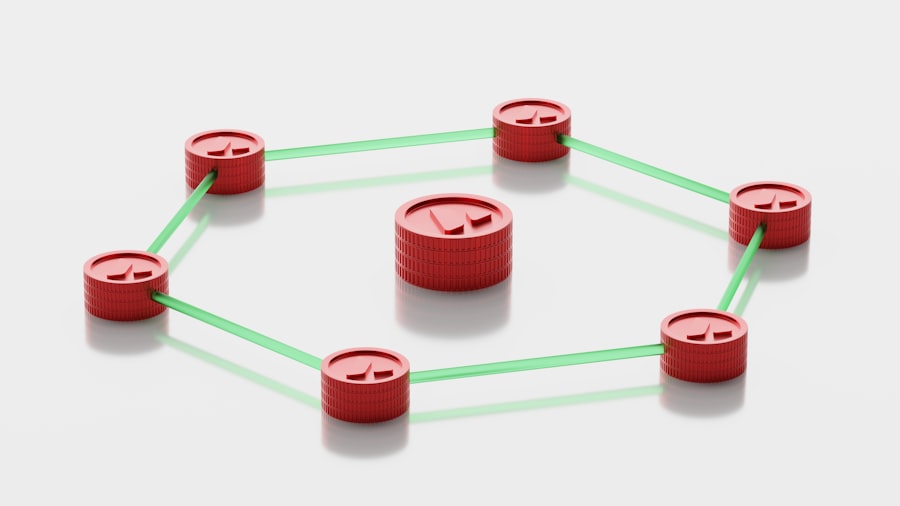
To effectively analyze packets, one must have a solid understanding of network protocols, which are the rules governing data communication over networks. Protocols dictate how data is formatted, transmitted, and received, ensuring that devices can communicate seamlessly. The Internet Protocol (IP), Transmission Control Protocol (TCP), and User Datagram Protocol (UDP) are foundational protocols that form the backbone of internet communication.
IP is responsible for addressing and routing packets between devices, while TCP ensures reliable transmission by establishing connections and managing data flow. UDP, on the other hand, offers a connectionless alternative that prioritizes speed over reliability, making it suitable for applications like video streaming and online gaming. Each protocol operates at different layers of the OSI (Open Systems Interconnection) model, which provides a framework for understanding how data travels through a network.
The OSI model consists of seven layers: physical, data link, network, transport, session, presentation, and application. Packet analysis often involves examining multiple layers to gain a comprehensive view of network activity. For example, analyzing packets at the transport layer can reveal information about connection establishment and termination processes, while examining application layer packets can provide insights into user interactions with software applications.
Understanding these protocols is essential for effective packet analysis because it enables analysts to identify anomalies or deviations from expected behavior. For instance, if an analyst observes an unusually high volume of UDP traffic on a network typically dominated by TCP traffic, it may indicate a potential issue or misuse of resources. Furthermore, familiarity with common protocols such as HTTP, FTP, and DNS allows analysts to interpret packet contents accurately and make informed decisions based on their findings.
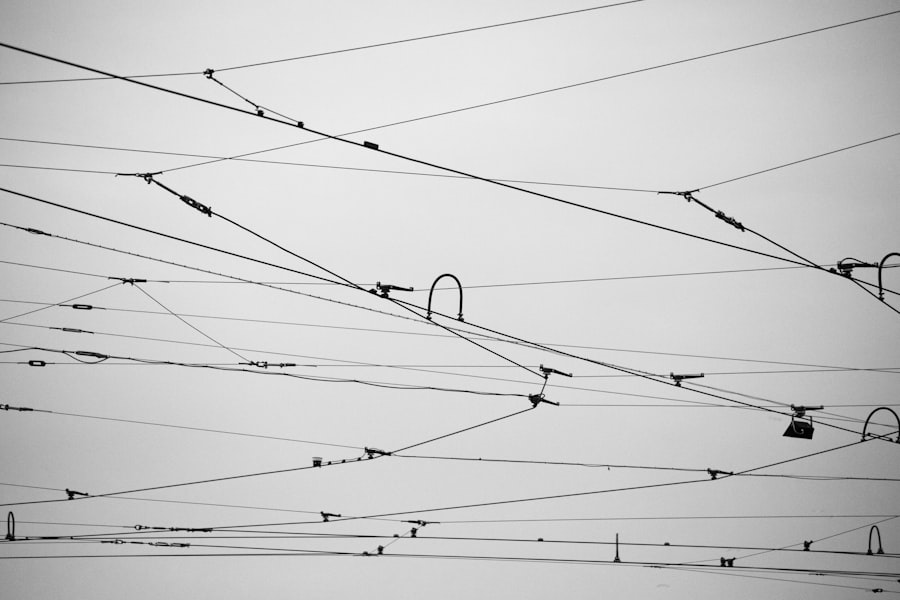
Identifying and Analyzing Network Traffic Patterns
Analyzing network traffic patterns is a fundamental aspect of packet analysis that can reveal valuable insights into user behavior and application performance. By examining traffic patterns over time, analysts can identify trends that may indicate normal usage or highlight potential issues that require attention. For instance, a sudden spike in traffic during off-peak hours could suggest unauthorized access or a denial-of-service attack.
Conversely, consistent patterns may indicate legitimate usage trends that can inform capacity planning and resource allocation. One effective technique for identifying traffic patterns is flow analysis, which involves monitoring the flow of packets between devices over time. Tools like NetFlow or sFlow can aggregate data from multiple sources to provide a holistic view of network activity.
By analyzing flow data, analysts can determine which applications consume the most bandwidth, identify peak usage times, and assess overall network health. This information is crucial for optimizing performance and ensuring that critical applications receive the necessary resources. Another important aspect of analyzing traffic patterns is understanding the relationship between different types of traffic.
For example, distinguishing between legitimate business-related traffic and potentially malicious activity requires careful examination of packet headers and payloads. Analysts may employ statistical methods or machine learning algorithms to detect anomalies in traffic patterns that deviate from established baselines. By leveraging these techniques, organizations can proactively address issues before they escalate into significant problems.
Troubleshooting Network Performance Issues
Packet analysis plays a pivotal role in troubleshooting network performance issues by providing detailed visibility into data transmission processes. When users report slow connections or application failures, packet analysis can help pinpoint the root cause by examining various factors such as latency, packet loss, and bandwidth utilization. For instance, if an analyst discovers high latency in TCP connections during peak usage times, it may indicate congestion on specific links or insufficient bandwidth allocation.
One common approach to troubleshooting involves using tools like Wireshark to capture packets during periods of reported issues. By analyzing these captures, analysts can identify patterns such as retransmissions or out-of-order packets that may signal underlying problems with network infrastructure or configuration. For example, if a significant number of TCP retransmissions are observed between two endpoints, it could suggest issues with network reliability or misconfigured devices along the path.
In addition to identifying immediate performance issues, packet analysis can also inform long-term strategies for improving network efficiency.
This proactive approach not only enhances user experience but also helps prevent future performance degradation by addressing potential bottlenecks before they impact operations.
Detecting and Analyzing Security Threats
The ability to detect and analyze security threats is one of the most critical applications of packet analysis in today’s cybersecurity landscape. As cyber threats become increasingly sophisticated, organizations must employ robust methods for identifying malicious activity within their networks. Packet analysis provides a powerful toolset for detecting anomalies that may indicate security breaches or attacks in progress.
One common method for threat detection involves monitoring for unusual patterns in network traffic that deviate from established baselines. For instance, an unexpected surge in outbound traffic from a specific device could suggest data exfiltration or a compromised system communicating with an external command-and-control server. By employing intrusion detection systems (IDS) that leverage packet analysis techniques, organizations can automate the identification of such anomalies and respond swiftly to potential threats.
Deep packet inspection (DPI) is another technique used to analyze packet contents for signs of malicious activity. DPI allows analysts to examine not only header information but also payload data within packets. This capability is particularly useful for identifying malware signatures or detecting unauthorized access attempts through specific protocols such as HTTP or FTP.
By analyzing payloads in real-time, organizations can implement measures to block malicious traffic before it reaches its intended target. Moreover, packet analysis can aid in forensic investigations following a security incident. By capturing packets during an attack or breach event, analysts can reconstruct the sequence of events leading up to the incident.
This information is invaluable for understanding how attackers gained access to systems and what vulnerabilities were exploited. Such insights not only help organizations strengthen their defenses but also contribute to broader efforts within the cybersecurity community to share threat intelligence and improve overall resilience against future attacks.
Case Studies and Real-World Examples
Real-world case studies illustrate the practical applications of packet analysis across various industries and scenarios. One notable example occurred during a major retail chain’s holiday shopping season when customers reported slow transaction processing at point-of-sale terminals. Network administrators utilized packet analysis tools to capture traffic during peak hours and discovered that excessive broadcast traffic from misconfigured devices was overwhelming the network infrastructure.
By isolating these devices and reconfiguring them appropriately, they were able to restore normal transaction speeds without significant downtime. Another compelling case involved a financial institution that experienced repeated unauthorized access attempts on its internal systems. Security analysts employed packet analysis techniques to monitor incoming traffic patterns closely.
They identified unusual spikes in login attempts from specific IP addresses associated with known malicious actors. By implementing firewall rules based on this intelligence and blocking these IP addresses proactively, the institution significantly reduced its exposure to potential breaches. In yet another instance, a healthcare organization faced challenges related to compliance with regulations governing patient data privacy.
Packet analysis was employed to monitor data flows between various systems handling sensitive patient information.
By implementing encryption protocols based on their findings from packet captures, the organization not only improved its security posture but also ensured adherence to regulatory requirements.
These case studies highlight how organizations across different sectors leverage packet analysis not only for troubleshooting but also as a proactive measure against security threats and compliance violations.
Best Practices for Packet Analysis
To maximize the effectiveness of packet analysis efforts, organizations should adhere to several best practices that enhance both accuracy and efficiency in their analyses. First and foremost is establishing clear objectives before initiating any packet capture activities. Understanding what specific issues need addressing—whether performance-related or security-focused—guides analysts in selecting appropriate tools and techniques tailored to those goals.
Another best practice involves maintaining proper documentation throughout the packet analysis process. Keeping detailed records of captured packets—including timestamps, source/destination IP addresses, protocols used—enables analysts to track changes over time and facilitates collaboration among team members during investigations or troubleshooting efforts. Additionally, organizations should prioritize training for personnel involved in packet analysis activities.
Given the complexity of modern networks and evolving threat landscapes, continuous education ensures that analysts remain adept at using tools effectively while staying informed about emerging protocols or attack vectors. Finally, integrating packet analysis into broader network management strategies fosters a culture of proactive monitoring rather than reactive responses alone. Regularly scheduled analyses help identify trends early on—allowing organizations to address potential issues before they escalate into significant problems impacting operations or security.
By following these best practices alongside leveraging advanced tools and techniques available today—organizations can harness the full potential of packet analysis as an essential component within their overall IT strategy.
If you are interested in learning more about network security and packet analysis, you may want to check out the article “Hello World” on hellread.com. This article provides valuable insights into the basics of network security and can complement the information found in Practical Packet Analysis by Chris Sanders. By exploring different perspectives and resources, you can enhance your understanding of this important topic and improve your skills in analyzing network traffic.
FAQs
What is packet analysis?
Packet analysis is the process of capturing and analyzing data packets that are transmitted over a network. It involves examining the contents of the packets to understand network behavior, troubleshoot network issues, and identify security threats.
What are the benefits of packet analysis?
Packet analysis provides valuable insights into network performance, helps in troubleshooting network issues, and aids in identifying and mitigating security threats. It also helps in understanding network traffic patterns and optimizing network infrastructure.
What tools are commonly used for packet analysis?
Commonly used tools for packet analysis include Wireshark, tcpdump, and Microsoft Network Monitor. These tools allow users to capture, analyze, and interpret network packets to gain insights into network behavior and troubleshoot issues.
What are some common use cases for packet analysis?
Packet analysis is commonly used for troubleshooting network performance issues, identifying the root cause of network outages, analyzing network security incidents, and optimizing network infrastructure. It is also used for monitoring and analyzing network traffic patterns.
What skills are required for effective packet analysis?
Effective packet analysis requires a good understanding of networking protocols, the ability to interpret packet contents, and knowledge of common network troubleshooting techniques. Additionally, familiarity with packet analysis tools and the ability to analyze and interpret network traffic patterns are essential skills for effective packet analysis.